Leave your phone at the door: side channels that reveal factory floor secrets Hojjati et al. CCS ’16
Here’s another reminder of just how powerful modern phones are as espionage devices, packed full of sensors. The short version is that if you place a phone near a manufacturing device (CNC mill or 3D printer in the demonstrated attacks), or even just make a phone call to someone standing near one of those machines on the factory floor, then you can gather enough information from the phone sensors to reconstruct the object being fabricated!
Manufacturing know-how is high-value IP. In 2014, 21% of manufacturers reported a loss of intellectual property due to cyberattacks (and the actually observed attacks are probably just the tip of the iceberg). In 2015, the incidents reported to the Industrial Control Systems Cyber Emergency Response Team operated by the US Department of Homeland Security grew by more than 50%.
IP theft is by far the most common motive of the attackers, who can target product design information, manufacturing process information, or both. The advantage of stealing design information is clear, but many manufacturer’s competitive advantage largely lies in the fact that they know how to manufacture a given design better, faster, or cheaper than their competitors do.
There are lots of ways to get malware onto phones (for example, the Shedun Android malware provides a framework to download and install malware and is considered nearly impossible to remove completely). With a malicious app installed, a simple geofence around a factory could be used to activate malware recording, which could run in the background of another app. If that’s all too much hassle, you just need to know the phone number of an employee who works the machine, call them up, and keep them talking for a while!
Milling and printing
As no single paper can reconstruct all process parameters for all major types of equipment, we focus on key parameters related to the location of the tool head with respect to the object being fabricated and its direction of travel. These location and direction parameters are important for both additive and subtractive manufacturing, and must be specified to control machines as disparate as a 3D printer and a CNC mill…
If you can recover the tool head location and direction, then you can recover the part being fabricated. Machines have different constraints in how they traverse the 3D space, which aids in recovery. For example a 3D printer works layer by layer, and emits a characteristic sound when it moves up on the Z axis. In between these movements, the challenge is reduce to detection location and direction just in the XY plane. Furthermore, since each layer must overlap the previous layer or have its own support material, these constraints further narrow the search space.
A printer’s audio signature changes at different angles within the XY plane. Here’s some example sensor data from 3D printing a square layer:
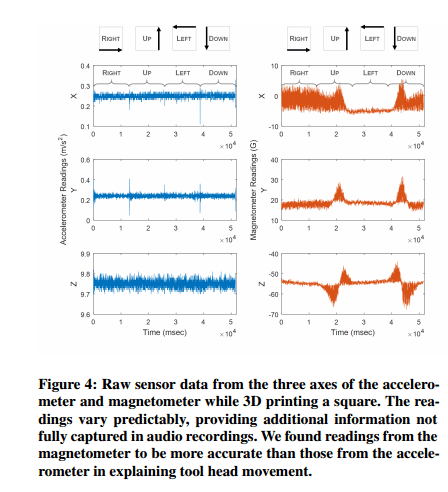
The reconstruction method uses audio and magnetometer data when both are available, and just audio otherwise. When multiple reconstructed objects are consistent with the results produced by signal processing and machine learning, the reconstruction method uses a search process, domain constraints, and human assistance to rule out unlikely and impossible reconstructions.
Preparation
In order to determine the angle of travel of the machine, a pre-recorded reference library of the sounds the machine makes at each angle (the authors record in 1-degree increments) is needed to compare the recorded sounds to. There are two ways to get the reference sounds: either record them from a similar machine model to the one being targeted, or cause the target machine to fabricate an object in which the necessary calibration pattern is hidden.
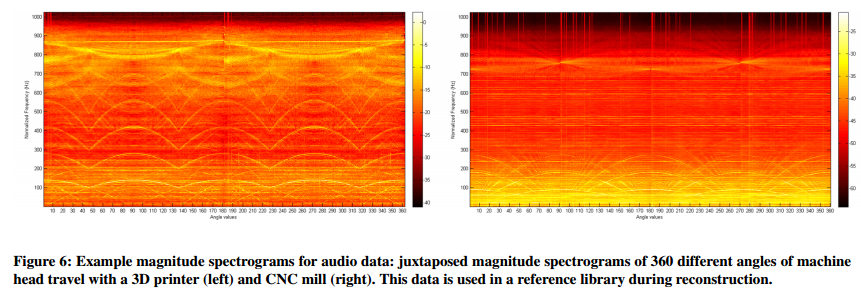
The sound is recorded using a cell phone, and then transformed to the frequency domain using a short time Fourier Transform. The matlab spectrogram function was then used to produce a spectrogram. If the recording was made in a manufacturing environment there is likely to be background noise, this is reduced by performing noise normalization in the frequency domain, based on a portion of the recording when the machine is idle.
To further reduce the effect of background noise and unwanted interference in the library, we average all the frames of the signal of the same angle along the time dimension of the spectrogram. The result is 360 frames, corresponding to the 360 angles of movement illustrated in Figure 6. Each frame is the audio signature of the machine head at a particular angle across frequencies. Figure 6 shows that most of the information needed to decide what angle the machine is moving at is concentrated at low frequency bands. Further, signal artifacts such as aliasing are visible at high frequency bands. Therefore we select only frequencies below a cutoff frequency f<sub>c</sub> for further processing, saving the results in the reference library.
Signal processing and reconstruction
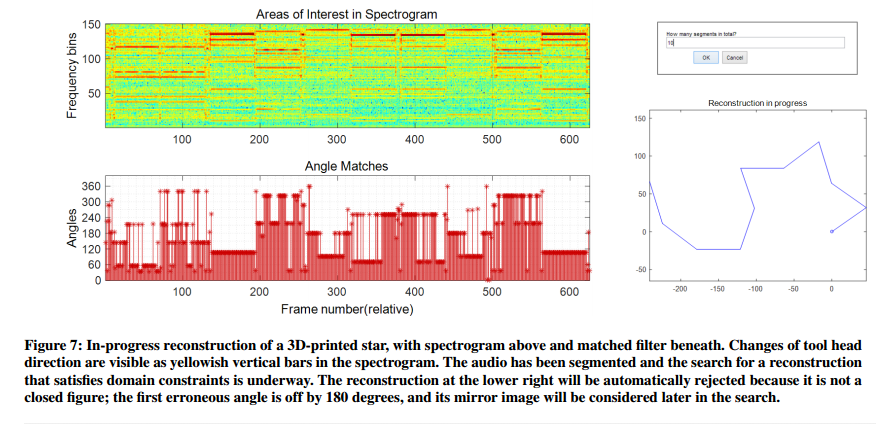
Reconstruction from a captured signal begins as for creating the reference signals: defining overlapping frames, producing a magnitude spectrogram, normalizing with respect to background noise, and retaining only the relevant frequency band. Then the most likely angle for each frame is found by comparing to the reference library.
More precisely, we use a custom matched filter function to compute the correlation between the audio frame and each of the reference library frames; this is a standard technique for comparing two audio samples. The result is one value for each combination of target audio frame and a library angle. For each target audio frame, we select the library angle with the highest cross correlation value for that frame: this is our best guess angle for that moment of the fabrication. Then we present the results to the user as shown in Figure 7’s screenshot of our interactive reconstruction framework.
The current tool then relies on a human user to to divide the manufactured object into a number of straight line segments (by clicking on the points where the tool head changes angle – easily seen in the top part of figure 7, where each ‘column’ represents a segment). (It would be easy to automate this part of the task and probably get more accurate results in the process too).
The duration of each segment multiplied by the machine’s feed rate gives the physical length of each linear segment in the reconstructed shape, so the accuracy of segmentation affects the accuracy of the final reconstruction. In our experiments, we did not focus on trying to get segment lengths exactly right. We expect that signal processing techniques can be used to automate segmentation in the future, and may be more accurate than a human.
The user’s second task is then to guide the machine to speed up the search process. ” For example, suppose that the first choice angles for all segments do not produce a reconstruction. While the search process can automatically identify the segments with the most uncertainty in the matches, and automatically identify the second most likely angle for each, the user can also guide this process by clicking on the matched filter head heights (angles) that she would like the search to consider next. ”
A k-sided 3D printed object has an audio-only reconstruction space of roughly 4<sup>k</sup> potential objects. This drops to 2<sup>k</sup> if magnetometer readings are also available.
Fortunately, manufacturing domain constraints allow us to prune away most of the search space.
Experimental results
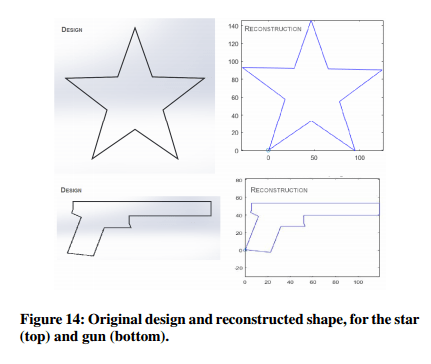
The team conducted tests with a variety of Android devices, and found that the Samsung Galaxy S6 worked best. Reconstruction effectiveness was tested with a variety of shapes including an airplane, star, and a gun. Users of the reconstruction software who had no previous idea of the shape they were trying to reconstruct where successfully able to recover all three.
Using a CNC mill and a 3D printer to represent subtractive and additive manufacturing, respectively, we demonstrated that ordinary mobile phones can effectively capture these machines’ acoustic and electromagnetic information on a factory floor, and the recordings can be used to reconstruct the objects being manufactured and the processes used to make them…. As mobile phones are ubiquitous, so is the potential for carrying out phone-based attacks, regardless of the state of IT security in a factory floor’s systems. Phone recordings may be made deliberately by an attacker or inadvertently by an individual with a compromised application on their phone or other microphone enable device. Good audio data can even be captured in the background of a phone call placed or received on the factory floor.
Manufacturers should consider asking their employees and visitors to leave their phones at the factory door…
Hi Adrian,
I enjoy reading your blog very much. I wonder, can you sometimes write a post about how you select papers?
Hi Boris,
Glad you’ve been enjoying The Morning Paper. I wrote a little about how I select papers in this piece: https://blog.acolyer.org/2015/01/07/reflections-on-100-editions-of-themorningpaper/
Regards, Adrian.